Today I wanted to cover some command-line tips and tricks I’ve learned over the years to help me filter and analyze pcap files. The tools I will be using for this are TCPDump and TShark. The pcap I will be using is from https://www.malware-traffic-analysis.net. If you haven’t checked out this site yet you should because it is awesome. So lets begin.
An easy way to filter larger pcap’s is to use TCPDump. The following command line will read in a large pcap and then write out a smaller one:

tcpdump -n -r big.pcap -w http.pcap ‘port 80’
The first switch I use is -n which tells tcpdump not to resolve dns. The -r switch reads in the pcap and -w writes out the new one and finally ‘port 80’ is a Berkeley Packet Filter that is filtering out all traffic on port 80.
The other tool I also wanted to mention is tshark. It is a great tool that can literally give you most of Wiresharks functionality at the command-line. This tool will allow you to pick and choose the fields you would like for the pcap. The following command line will read in your pcap with no dns resolution and spit out the fields you specify in the pcap:
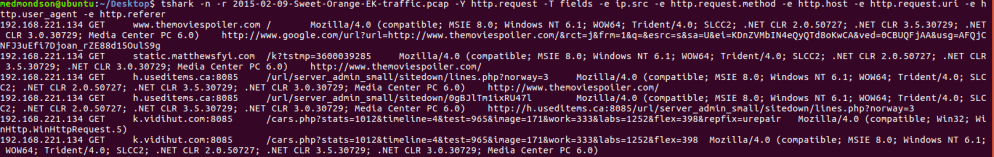
tshark -n -r 2015-02-09-Sweet-Orange-EK-traffic.pcap -Y http.request -T fields -e ip.src -e http.request.method -e http.host -e http.request.uri -e http.user_agent -e http.referer
The next command shows how you can pipe your tshark commands into sed, which is a pretty powerful technique. All I did here was read in my pcap with no dns resolution and used a display filter to pull out packets containing vidihut.com with a uri that has .php in it. Then I use sed to only show me the text after ‘stats=’. Your imagination is your only limit when you start piping Linux commands.
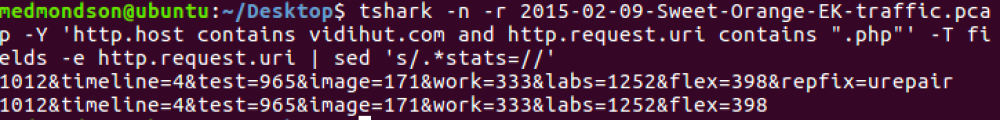
tshark -n -r 2015-02-09-Sweet-Orange-EK-traffic.pcap -Y ‘http.host contains vidihut.com and http.request.uri contains “.php”‘ -T fields -e http.request.uri | sed ‘s/.*stats=//’
The last command I will leave you with will pull out all of the http host and sort and uniq them by count.

tshark -n -r 2015-02-09-Sweet-Orange-EK-traffic.pcap -Y http.request -T fields -e http.host | sort | uniq -c | sort -nr
These were just a handful of the cool things you can do on the Linux command line to help you slice and dice your pcap’s to help you find evil. So until next time.
Happy Hunting,
Marcus