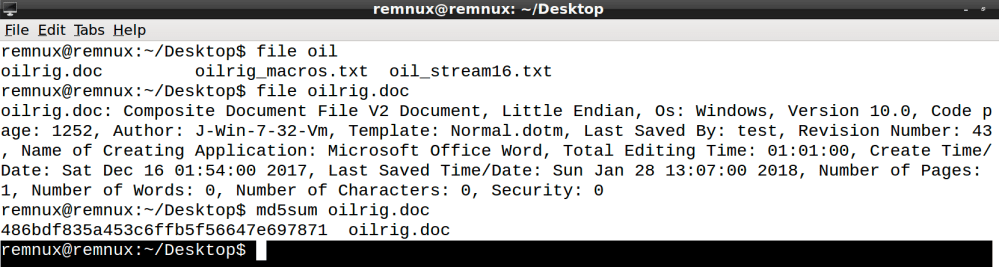
So today I wanted to analyze a Microsoft Word document I downloaded from 0xffff0800 .onion website http://iec56w4ibovnb4wc.onion and just go through some quick triage steps to strip out some Indicators of Compromise (IOC’s) if you needed to start scanning your environment quickly. So as usual, when I pull down a sample I will transfer it to my Remnux box to run the file command and md5sum to find out what type of file I’m dealing with and get a hash.
Once I know the type of file I’m working with and have a hash which can be used as an initial IOC to give to the IR team, I will want to see if there are any embedded macros or anything interesting. For this step I will be using oledump.
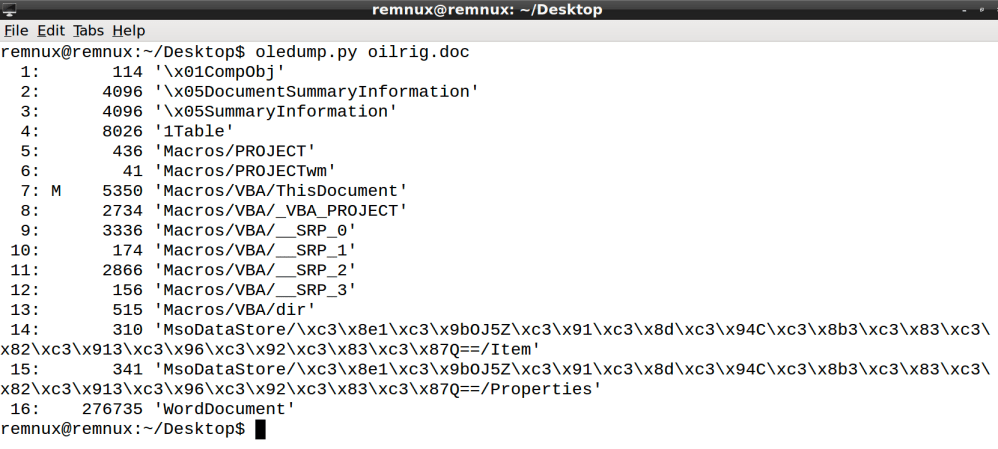
After running oledump I can see we do have embedded macros and we also have something that at first glance appears to look like shellcode and in stream 16 WordDocument looks interesting due to its size. The SRP streams could also be of interest because they store compiled versions of VBA macros. So basically they might contain cached copies that were present in earlier versions of the document. I will use the oledump tool to dump the macros.

Taking a quick look at the macros it appears to some sort of dropper, my VB skills are not great but it looks to be creating a PowerShell file named AdobeAcrobatLicenseVerify.ps1. It also looks to be creating a scheduled task named “Conhost”. So this got me thinking that there could be a PowerShell script somewhere in this document. I initially looked through the SRP streams and did not find anything that resembled a PowerShell script. I then used olebrowse to look at the large stream named WordDocument.

That certainly looks like a PowerShell script to me. I’m sure there is a cleaner way of doing this and in the future I’m going to purchase Microsoft Office so I can actually run the document to see how it behaves, but for now this will have to work. I then just carved out the script and pasted it into PowerShell_ISE to take a look at it.

So this is what I was able to carve out using the hex editor. Taking a quick glance to strip out some IOC’s I can see it looks like a registry key named AdobeAcrobatLicenseVerify in the HKCU hive is created. It also appears to delete our scheduled task named Conhost, which might be it cleaning up after itself. We also have a domain name of acrobatverify.com which looks to be a possible malicious site according to Kaspersky and Fortinet. Some other IOC’s that could be pulled out are the user agents in the script. I definitely will be buying Microsoft Office really soon so I can actually run these samples in my VM. If you know of a good way to dump out this script in order to run it please leave a comment below and until next time…
Happy hunting,
Marcus
One thought on “APT34 OilrigThreeDollarsMacro.doc Analysis”