Today I wanted to do a blog post on unpacking Shade (Troldesh) ransomware md5 7F9D970C685F7F33AA8A961F2A10173D. The sample I used was acquired from here. Troldesh is a crypto ransomware variant that was created in Russia. So the short story is it will encrypt your files and try to extort money from you. The technique I used on this sample was to set two breakpoints, one on VirtualAlloc which according to Microsoft MSDN, this API reserves, commits, or changes the state of a region of pages in the virtual address space of the calling process. Memory allocated by this function is automatically initialized to zero. The second breakpoint we will set on the return from VirtualAlloc, which I will then dump the EAX register which by convention is where VirtualAlloc will store it’s info. Let’ begin…
The first step I took was to load the sample into PEStudio to get a look at some of it’s metadata to include strings and imports, and then load it into exeinfo to see if there is any known packer detection.
So according to exeinfo it does not appear to packed but I have a suspicion we will find some extra stuff tucked away in this sample. So let’s load it up into x32dbg and see what we can find. So like I said earlier we want to set breakpoints on VirtualAlloc and its return. I picked this technique up from watching the videos from the guys over at OALabs on youtube. If you haven’t checked out there stuff you should it’s great! 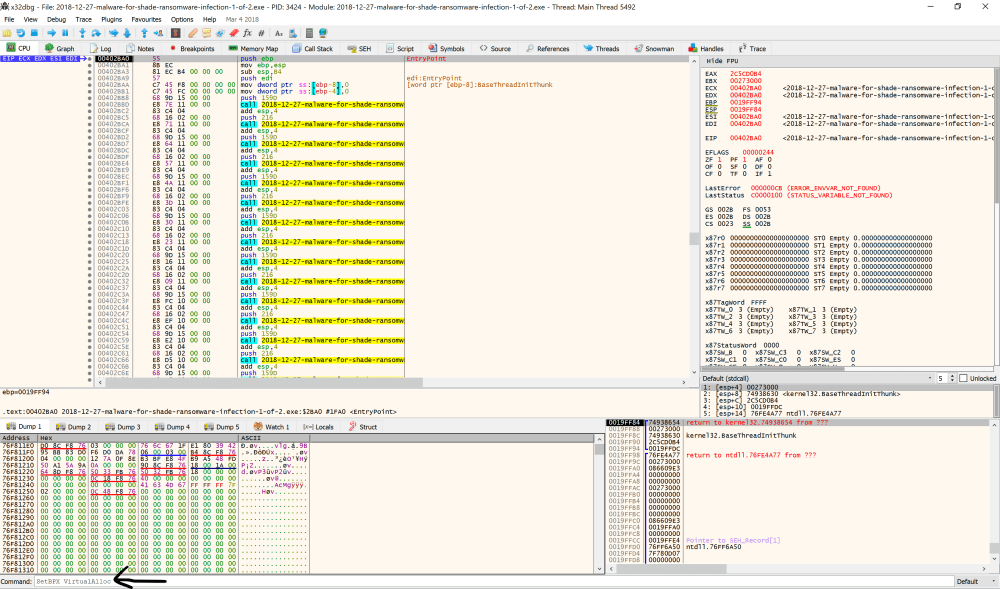
Once you get your command typed in press enter and go up to debug in the toolbar and click run or F9 will also run the sample. Let’s see if we hit our breakpoint…
Once you hit your breakpoint start single stepping until you take the jump pointed to by the arrow.
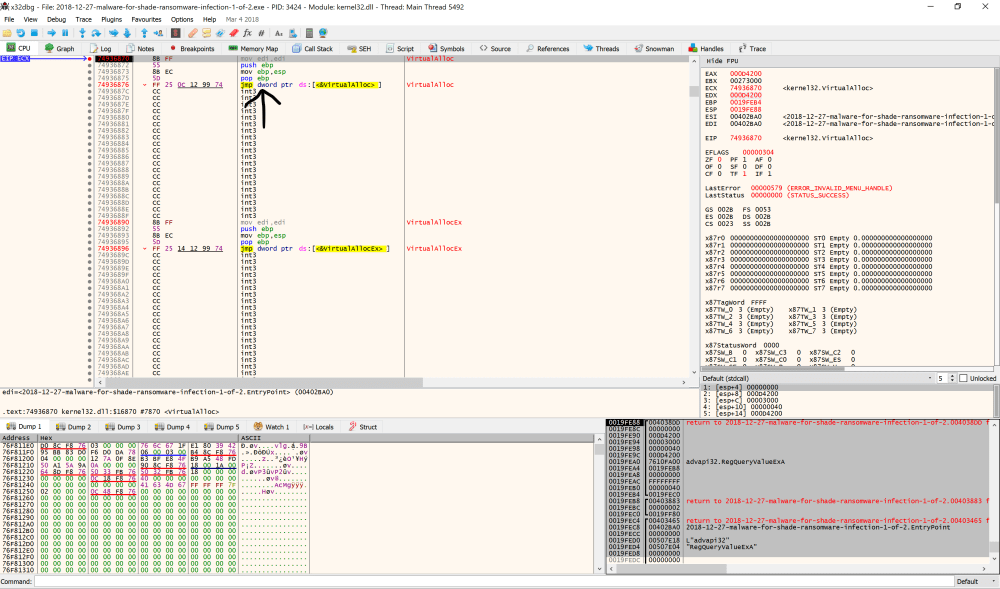
Once you take the jump set a breakpoint, to set this breakpoint just highlight return and press F2 on the first ret and then click run. You will then click on the EAX register and follow it’s contents in a dump…

So the contents of the EAX register have been zeroed out which is how VirtualAlloc will allocate memory space. From here we will keep an eye on this dump and click run until VirtualAlloc is not called anymore.

So it looks like we have some really interesting API calls that we did not see earlier and a garbled string that looks like it could be “This program can not be run in DOS mode” lets keep dumping.
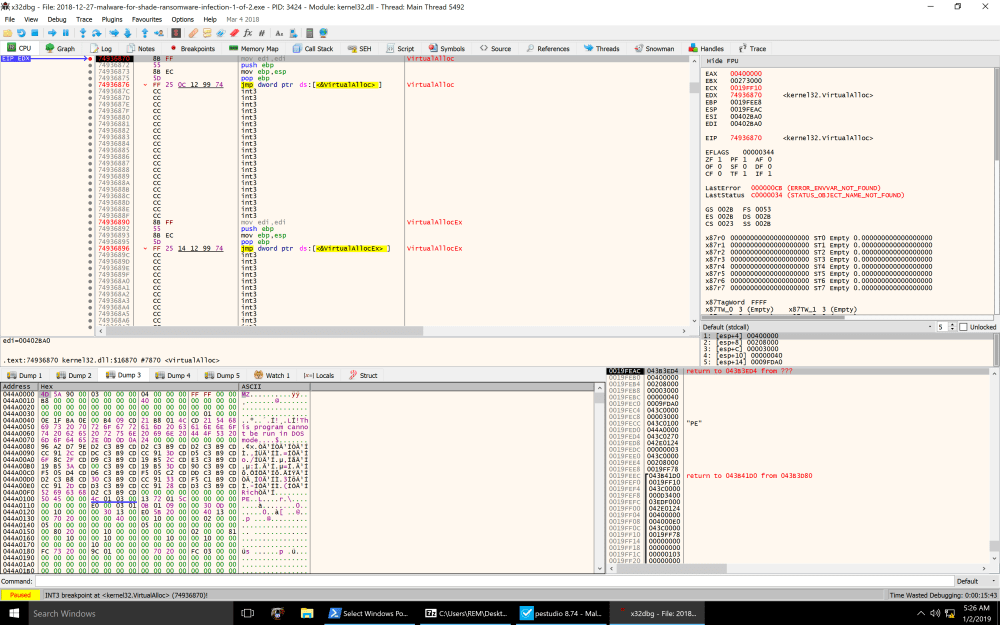
And we have a PE! Keep using this technique and with each consecutive breakpoint and return dump the content of EAX to your different dump sections below. You should be able to dump out 2 additional executables which are packed with UPX. So thank you for reading and until next time…
Happy Hunting,
Marcus